Guide to Spotting the Microsoft Security Alert Email Scam 2025
Learn how to spot the microsoft security alert email scam in 2025 with expert tips, red flags, real examples, and proven strategies to keep your data safe.
Have you received a suspicious email claiming to be a microsoft security alert email scam? You are not alone. Millions of users worldwide face these deceptive messages in their inboxes every year.
This guide is your trusted resource for 2025, designed to help you spot, verify, and avoid the latest microsoft security alert email scam attempts. We will break down the mechanics of these scams, reveal new red flags, and share expert steps to keep your data safe.
With attacks growing more sophisticated, protecting your personal and business information is crucial. By following this guide, you will gain the knowledge and confidence to outsmart scammers. Stay informed, apply our strategies, and help others in your network stay safe from the microsoft security alert email scam.
Understanding the Microsoft Security Alert Email Scam
Have you ever wondered why the microsoft security alert email scam is so widespread? As digital threats evolve, this scam has become a prime method for cybercriminals to target both individuals and organizations. In 2024 alone, more than 85 percent of users reported receiving fake Microsoft security alerts, making it one of the most common phishing threats globally.

The Rise of Microsoft-Themed Phishing Attacks
The microsoft security alert email scam has surged due to Microsoft’s massive user base and the value of its accounts. With Outlook ranking third in global email market share, attackers have a vast pool of potential targets. Microsoft accounts often store sensitive business and personal information, making them especially attractive.
Scammers exploit the trust users place in Microsoft’s brand and the integration of Microsoft tools in daily workflows. The shift to remote and hybrid work has expanded the attack surface, as employees connect from less secure networks and devices. For example, a recent case involved a phishing email from a sender mimicking ‘account-security-noreply@accountprotection.microsoft.com.’ Users who followed the link ended up on a convincing fake site, resulting in credential theft.
These scams rely on fear and urgency. Messages often state that your account will be suspended or compromised unless you act immediately. This psychological pressure makes even tech-savvy users more likely to fall for the microsoft security alert email scam.
How the Scam Works
The typical journey of the microsoft security alert email scam begins when a user receives a message claiming to be from Microsoft. The email contains urgent warnings about account security, prompting the user to click a link or open an attachment. Once clicked, victims are taken to a spoofed login page that visually matches Microsoft’s official site. Entering credentials here gives attackers direct access to accounts.
Cybercriminals have refined their tactics, using lookalike domains and near-perfect branding to avoid detection. Some emails reference recent Microsoft security breaches or news, making the message seem timely and authentic. Social engineering techniques are common, with scammers sometimes including real user data or referencing recent activities to gain trust.
Attachments are another threat vector in the microsoft security alert email scam. Files disguised as “account verification” forms or “security reports” may contain malware that infects the victim’s device, leading to data loss or system compromise.
Why These Scams Are So Effective
The effectiveness of the microsoft security alert email scam lies in its realism. Attackers use official-looking sender addresses and replicate Microsoft’s branding with remarkable accuracy. Many scams eliminate spelling and grammar errors, further reducing suspicion.
Scammers also exploit legitimate Microsoft security features. Emails may reference two-factor authentication alerts or password reset notifications, mirroring real communications. The average user, without specialized training, can find it challenging to spot subtle inconsistencies.
What makes matters worse is the sophistication of these attacks. As phishing techniques evolve, even experienced professionals can be fooled. To help you stay ahead, consult Microsoft's official phishing protection guidelines for practical steps to recognize and avoid these scams.
Understanding why the microsoft security alert email scam works is the first step in defending yourself and your organization against these persistent threats.
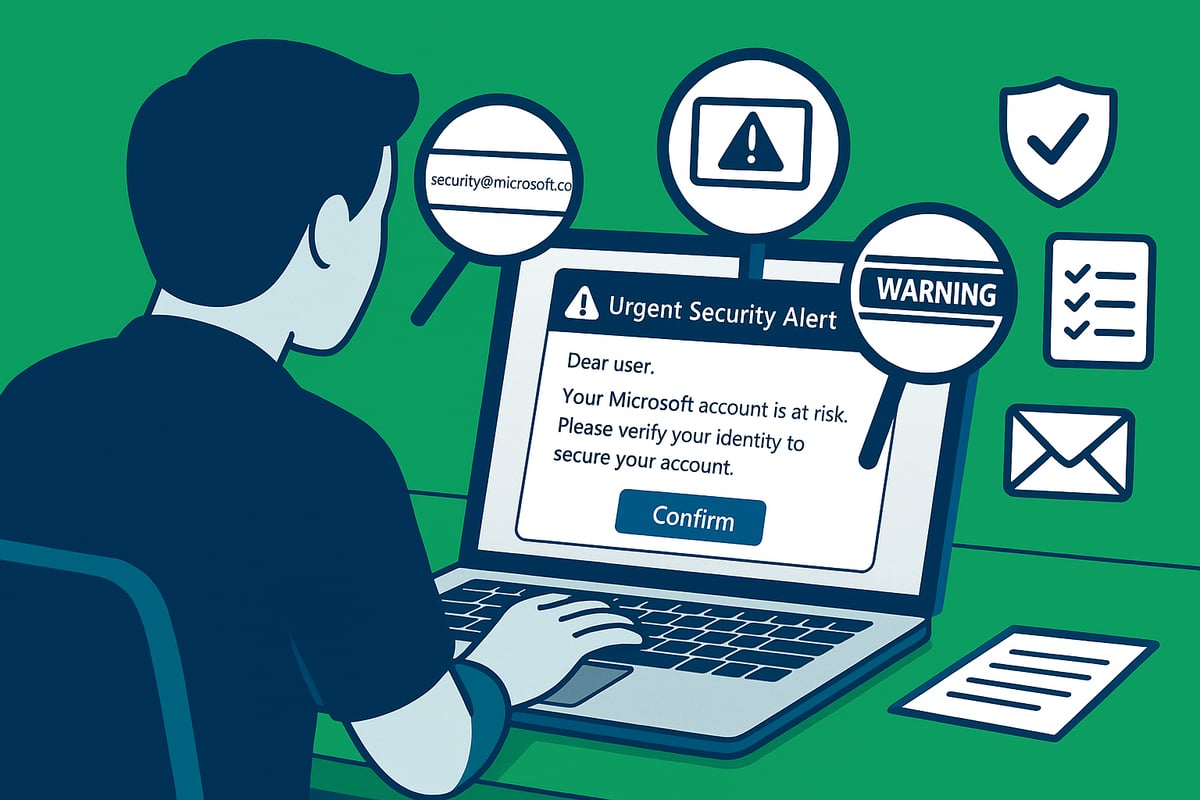
Key Red Flags: How to Identify a Fake Microsoft Security Alert Email
Have you ever wondered how to tell if a microsoft security alert email scam has landed in your inbox? Recognizing the red flags is essential, as scammers are becoming more sophisticated every year. Below, we break down the most common warning signs so you can defend yourself and your organization confidently.

Sender and Domain Analysis
The first clue in spotting a microsoft security alert email scam often lies in the sender address. Genuine alerts from Microsoft come from addresses ending with @accountprotection.microsoft.com. Scammers try to mimic these but usually introduce subtle changes like extra letters, numbers, or misspellings.
To verify authenticity:
- Hover over the sender name to reveal the actual email address.
- Look for extra characters or domains that are close but not exact, such as
@accountprotection-micr0soft.com. - Check for personalized greetings. Microsoft rarely uses generic phrases like "Dear User." Instead, they typically address you by name.
A quick glance at the sender can save you from falling victim to a microsoft security alert email scam. Always question emails that seem even slightly off.
Visual and Textual Cues
Scammers have improved their design skills, but many fake emails still have visual flaws. Compare the look and feel of the message to previous legitimate Microsoft emails.
Tell-tale signs include:
- Poor grammar or awkward phrasing
- Inconsistent fonts or strange color schemes
- Low-resolution or distorted Microsoft logos
- Unusual formatting or layout errors
Authentic Microsoft emails maintain a high standard of professionalism. If a message looks sloppy, treat it as a potential microsoft security alert email scam.
Suspicious Content and Links
The content of a microsoft security alert email scam is often urgent or alarming. Messages may claim your account will be suspended unless you act immediately, or prompt you to verify sensitive details.
Be wary if you notice:
- Requests for personal information, passwords, or 2FA codes (Microsoft never asks for these via email)
- Links that, when hovered over, do not lead to an official Microsoft domain
- Attachments labeled as "security reports" or "account verification"
If you receive an unexpected file or are asked to click a suspicious link, pause before taking any action. These are classic hallmarks of a microsoft security alert email scam.
Verification Indicators and Warnings
Modern email clients like Outlook and Gmail have built-in security features to help you spot scams. Microsoft may flag suspicious emails with a question mark or display a warning banner for unverified senders.
To verify:
- Look for security banners or warning icons in your inbox
- Compare the tone and branding with previous legitimate Microsoft alerts
- Check for inconsistencies in messaging or formatting
These subtle cues can reveal a microsoft security alert email scam before any damage is done. When in doubt, cross-reference with emails you know are genuine.
Real-World Examples and Statistics
Recent phishing campaigns have leveraged near-identical sender addresses and layouts, resulting in thousands of compromised accounts. In 2024, targeted security training led to a 60% drop in successful scams, showing that awareness is key.
For more prevention strategies, explore these Microsoft phishing protection tips to stay ahead of evolving threats.
Remember, even a single click on a fake microsoft security alert email scam can have serious consequences. Stay vigilant and share these red flags with your team to help everyone stay protected.
Step-by-Step Guide: Verifying the Authenticity of a Microsoft Security Alert Email
Have you received a suspicious Microsoft security alert email scam and wondered if it was real? Following a methodical process can help you avoid falling victim to these increasingly sophisticated attacks. Use the detailed steps below to keep yourself and your organization safe.
Step 1: Pause and Assess the Email’s Context
When you first spot a Microsoft security alert email scam, stop and think before taking action. Ask yourself if you recently performed any activity that would trigger a security notice. Did you request a password reset or attempt to log in from a new device? Scammers rely on panic and urgency, so taking a moment to assess the context is your first defense.
If the message seems out of place, do not interact with any links or attachments. Cross-reference the information with your recent Microsoft account activity by logging in directly through your browser. This initial pause helps prevent impulsive mistakes.
Step 2: Examine the Sender and Headers
A common sign of a Microsoft security alert email scam is a sender address that looks almost legitimate but contains subtle errors. Check for misspellings, extra characters, or domains that are not associated with Microsoft. For example, a real alert comes from @accountprotection.microsoft.com, while a scam might use @accountprotect1on-microsoft.com.
For advanced users, inspect the full email headers to spot anomalies such as mismatched reply-to addresses or unexpected routing paths. If something seems off, treat the message with suspicion.
Step 3: Scrutinize Links and Attachments
Before clicking anything, hover your mouse over all links in the suspected Microsoft security alert email scam. Examine the URL preview that appears. Legitimate links will always point to official Microsoft domains, such as https://account.microsoft.com. Be cautious of lookalike domains, extra characters, or shortened URLs.
Do not download any attachments unless you are certain they are safe. Attachments in these scams often contain malware or ransomware. For added protection, consider solutions like real-time email threat detection that automatically analyze incoming messages and flag suspicious links and files.
Step 4: Check for Microsoft’s Security Indicators
Genuine Microsoft alerts include visual security cues, such as verified sender icons, warning banners, and consistent branding. Pay attention to any “unverified sender” tags, question marks, or banners indicating the message might be suspicious. Compare the look and tone of the email with previous legitimate alerts you have received.
If the Microsoft security alert email scam lacks professional formatting or includes odd color schemes, treat it with caution. Consistency is key to authentic communication from Microsoft.
Step 5: Log in Directly via Official Channels
Never click links inside a potential Microsoft security alert email scam. Instead, open your web browser and manually type https://account.microsoft.com. Once logged in, check the ‘Recent Activity’ section for any unfamiliar logins or changes.
If there is truly a security issue, you will see notifications or alerts in your account dashboard. This approach ensures you are interacting only with trusted channels and not a spoofed website.
Step 6: Cross-Verify with Microsoft Support or Community
If you are still unsure whether a Microsoft security alert email scam is real, reach out to Microsoft’s official support. Use verified contact methods found on Microsoft’s website, not those provided in the email. You can also search online or ask in official Microsoft community forums about similar scam reports.
If others have reported the same suspicious email, it is almost certainly a phishing attempt. Collective intelligence can be a powerful tool in identifying widespread scams.
Step 7: Report and Delete Suspicious Emails
Once you have determined a message is a Microsoft security alert email scam, report it using your email provider’s “Report phishing” or “Mark as spam” feature. This helps improve filtering for you and others.
After reporting, delete the email from your inbox. Never reply or engage with the sender. Taking these actions not only protects you but also contributes to a safer digital environment for everyone.
Common Types of Microsoft Security Alert Email Scams in 2025
Have you noticed a sudden spike in suspicious messages claiming to be from Microsoft? You are not alone. The microsoft security alert email scam has evolved dramatically in 2025, targeting both individuals and organizations with new tactics. Understanding the main types of these scams is key to staying protected.
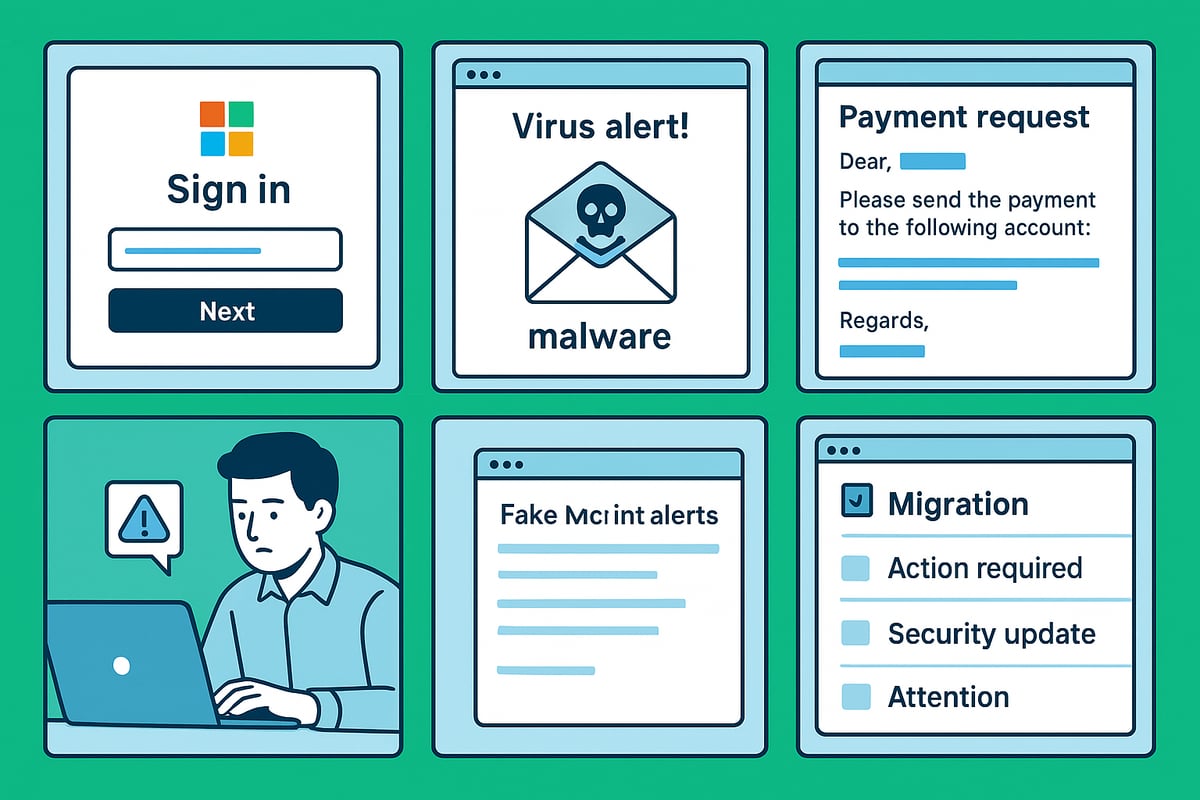
Phishing Attacks
Phishing remains the most prevalent microsoft security alert email scam. Attackers send emails disguised as urgent security alerts, prompting users to "verify" their accounts. These messages often contain links to fake Microsoft login pages. If a user enters their credentials, scammers instantly gain access to sensitive information.
- Lookalike domains closely mimic official Microsoft URLs.
- Urgent language, such as "immediate password reset required," pressures recipients.
- Example: In 2024, remote workers received fake password reset alerts, leading to mass credential theft.
These attacks are highly effective because they exploit both trust and urgency.
Malware and Spyware Delivery
Another common microsoft security alert email scam involves hidden malware or spyware. Attackers attach malicious files labeled as "security reports" or "account verification forms." Opening these files can install ransomware or spyware, compromising both personal and company data.
- Attachments may appear as PDFs or Office documents.
- Malware can steal credentials, encrypt data, or surveil user activity.
- In one case, thousands were infected after opening a "Microsoft security update" attachment.
Always treat unexpected files in security alert emails as suspicious.
Business Email Compromise (BEC)
The microsoft security alert email scam has also expanded into business email compromise. Scammers impersonate Microsoft support to deceive employees, aiming to extract credentials or even trick staff into transferring company funds. These attacks target both small businesses and large enterprises.
- Emails are well-crafted, often referencing real IT issues or company news.
- Attackers may request urgent account changes or wire transfers.
- BEC scams have resulted in billions in global losses, with Microsoft-branded emails among the leading lures.
Vigilance and internal verification protocols are essential in preventing BEC incidents.
Social Engineering and Remote Work Threats
Social engineering is a critical component of the microsoft security alert email scam, especially with the rise in remote work. Attackers reference recent company events or mimic internal announcements to appear credible. They exploit weaker home security setups and encourage bypassing standard IT protocols.
- Emails may mention recent layoffs, security breaches, or policy updates.
- Remote employees are more likely to respond quickly, increasing risk.
- Attackers use personal details to make messages more convincing.
Companies must educate remote workers on these evolving tactics.
Spoofed Alerts and Bulk Campaigns
Bulk email campaigns are another hallmark of the microsoft security alert email scam. Attackers use automated tools to send out thousands of fake alerts at once, increasing the odds of success. Multiple users within the same organization may receive identical scam emails simultaneously.
- Spoofed sender addresses often contain subtle misspellings or extra characters.
- Bulk campaigns can overwhelm spam filters if not properly configured.
- These attacks are designed for scale, relying on a small percentage of victims to succeed.
Robust email filtering and user awareness are key defenses.
Statistics and Trends
In 2024 and 2025, the microsoft security alert email scam has surged alongside global increases in remote and hybrid work. According to industry reports, phishing attacks using Microsoft branding have reached record highs. In a notable case, Microsoft seized 340 phishing websites linked to a large-scale subscription scam, demonstrating the scale and sophistication of these threats.
Security awareness training has proven highly effective, reducing successful phishing attempts by up to 60 percent. Organizations that regularly educate employees about the latest scam trends experience fewer breaches and faster response times.
Understanding the diverse forms of the microsoft security alert email scam is the first step in proactive defense. By recognizing these tactics, you can better safeguard your personal and business data from evolving cyber threats.
Proactive Strategies: Preventing Microsoft Security Alert Email Scams
Staying ahead of the microsoft security alert email scam takes more than luck. It requires a blend of technical measures, training, and ongoing vigilance. Here are proven strategies to help you and your organization remain protected in 2025.
Strengthen Account Security
The first step in defending against the microsoft security alert email scam is robust account security. Set strong, unique passwords for every Microsoft account. Use a mix of uppercase and lowercase letters, numbers, and symbols. Avoid common phrases or reused passwords.
Enable multi-factor authentication (MFA) across all Microsoft services. This extra step dramatically reduces the risk of unauthorized access, even if your password is compromised. Regularly review your account's sign-in activity and remove unfamiliar devices. These habits form the foundation of your security posture.
Keep Software and Security Features Updated
Outdated software often contains vulnerabilities that scammers exploit. To combat the microsoft security alert email scam, always install the latest updates for Windows, Office, and your email client. Updates patch security gaps that attackers target.
Leverage built-in protections such as Microsoft 365 Defender and Spoof Intelligence. These tools detect suspicious behaviors and attempt to block phishing attempts before they reach your inbox. Staying up to date keeps your defenses strong against evolving threats.
Optimize Email Settings and Filters
A well-configured inbox is a powerful line of defense against the microsoft security alert email scam. Enable advanced spam and phishing filters in Outlook, Gmail, or your preferred provider. Quarantine or block messages from unrecognized domains.
Consider using specialized email security tools for an added layer of protection. For example, About Ṣọ Email Security features details how their AI-powered extension can analyze every incoming email, flag suspicious messages, and help you spot Microsoft-themed scams in real time.
Ongoing Security Awareness and Training
Human error remains a top cause of security breaches. Regular security awareness training is essential for reducing the risk posed by the microsoft security alert email scam. Simulated phishing tests help users recognize real-world threats and build positive security habits.
Encourage your organization to create or update cybersecurity policies, especially for remote and hybrid workers. Stay informed about the latest social engineering tactics, including those powered by AI. According to recent studies, AI-driven phishing attacks increase effectiveness, making ongoing education more important than ever.
Be Skeptical of Unsolicited Requests
Scammers often succeed by exploiting trust and urgency. Never share passwords, 2FA codes, or sensitive information in response to any email request, even if it appears to reference a microsoft security alert email scam.
If you receive an unusual request, verify it through official channels. Avoid using links or contact details provided in the suspicious email. Instead, visit the official Microsoft website or reach out to your IT department directly.
Monitor Industry Trends and Scam Reports
The tactics used in the microsoft security alert email scam change rapidly. Monitor security advisories from Microsoft and leading cybersecurity organizations. Sharing new scam reports within your organization or network can help prevent others from falling victim.
Stay active in online communities and subscribe to security newsletters. Early awareness of emerging scams is often the key to avoiding them altogether.
Example Best Practices
A real-world example: A business received a suspicious security alert, but instead of reacting immediately, they checked with their IT team. This quick verification prevented a breach. Implement domain authentication protocols such as DMARC, SPF, and DKIM to stop attackers from spoofing your organization’s email address.
Smart, consistent application of these strategies is your best defense against evolving threats. Make them part of your routine and encourage others to do the same.
What to Do If You Suspect or Fall Victim to a Microsoft Security Alert Scam
Receiving a suspicious microsoft security alert email scam can be alarming, but acting swiftly and calmly makes all the difference. Whether you noticed red flags or accidentally clicked a link, following the right steps helps minimize risk and potential damage.
Immediate Actions for Individuals
If you suspect a microsoft security alert email scam, do not interact with the email. Do not click on any links or download attachments. Close the email immediately.
Change your Microsoft account password using the official Microsoft website. Enable or review your multi-factor authentication settings to add an extra layer of protection.
Check your ‘Recent Activity’ in your Microsoft account to identify any unauthorized logins or changes. Sign out of all unfamiliar sessions to prevent further access.
Reporting and Remediation Steps
Report the suspicious email as phishing using your email provider’s built-in tools. In Outlook or Gmail, use the “Report phishing” feature to alert security teams.
If you are using a work account, notify your IT or security department right away. File a report with Microsoft through their official scam reporting channels to help protect others.
For proactive protection against future threats, consider Getting started with scam protection to set up tools that automatically detect and block phishing attempts related to the microsoft security alert email scam.
System and Device Security Checks
Run a full antivirus and anti-malware scan on your device. Removing any detected threats is crucial to prevent further compromise.
If malware is found, consider seeking professional help to ensure your system is clean. Review your other accounts, such as banking or social media, especially if you reused passwords that were exposed by the microsoft security alert email scam.
Update your operating system and software to patch any vulnerabilities that attackers might exploit.
Organizational Response Protocols
If you are part of an organization and suspect a widespread scam, alert all users as soon as possible. IT teams should initiate a security audit to detect and contain any breaches.
Provide additional security training or reminders to staff about ongoing threats like the microsoft security alert email scam. Update response protocols to reflect the latest phishing tactics.
Encourage employees to follow company policies for verifying suspicious requests, especially those related to account security.
Learning and Prevention
After addressing the immediate threat, document the incident to identify what led to the exposure. Use this experience to update your security policies and awareness training.
Stay informed about evolving threats. Microsoft has introduced advanced detection features, such as their new scareware sensor to combat scams, which can help reduce the risk of falling for a microsoft security alert email scam.
Share insights and resources with colleagues and family members to strengthen collective awareness and resilience.
Real-World Example
Consider an employee who received a convincing microsoft security alert email scam but paused before reacting. By reporting the email to IT, they helped prevent a company-wide breach and reinforced the importance of vigilance.
Learning from these situations and applying the right steps ensures both individuals and organizations are better equipped to handle future threats.